Featured
Table of Contents
- – What Is A Vpn?how Does It Work?
- – What Is A Vpn And How Does It Work?
- – How Does A Vpn Work?
- – What Is Vpn - Virtual Private Network Definit...
- – What Is A Vpn?
- – Wtf Is A Vpn?
- – What Does Vpn Stand For?
- – What Is A Vpn? How Does It Work And Why Do Y...
- – What Is A Vpn And Why Do You Need One?
- – A Beginners Guide To Vpns - What Is A Vpn?
- – Virtual Private Network
What Is A Vpn?how Does It Work?
Anybody on the exact same network will not have the ability to see what a VPN user is doing. This makes VPNs a go-to tool for online privacy. A VPN utilizes tunneling procedures to secure data at the sending end and decrypts it at the receiving end. The coming from and getting network addresses are likewise secured to provide much better security for online activities.
The VPN client is not visible to the end user unless it creates performance issues. By utilizing a VPN tunnel, a user's gadget will link to another network, hiding its IP address and encrypting the information. This is what will hide private information from opponents or others intending to get access to a person's activities.
VPNs associate a user's search history with the VPN server's IP address. VPN services will have servers situated in different geographical areas, so it will appear like the user could be from any among those places. VPNs can affect performance in many ways, like the speed of users' web connections, the protocol types a VPN provider can use and the kind of encryption used.
What Is A Vpn And How Does It Work?
A kill switch is a last resort security feature in some VPN products. If the VPN connection is disrupted, the kill switch will automatically detach the device from the web to eliminate the opportunity of IP address exposure. There are two types of kill switches: prevent gadgets from linking to unsafe networks when the gadget is connected to the VPN.
They keep the gadget from connecting to non-VPN connections even while disconnected from the VPN server. VPNs are utilized for virtual personal privacy by both typical internet users and companies.
When surfing the web, an internet user might know accessed by an aggressor, consisting of browsing habits or IP address. If personal privacy is a concern, a VPN can provide users with assurance. File encryption, privacy and the ability to navigate geographically blocked material is what most users find important in a VPN.
How Does A Vpn Work?
The challenges of using a VPN, however, consist of the following: Not all gadgets may support a VPN. VPNs do not protect versus every risk.
Network administrators have a number of options when it comes to deploying a VPN that include the following. Remote access customers link to a VPN entrance server on the organization's network. The entrance requires the gadget to validate its identity prior to approving access to internal network resources. This type usually depends on either IPsec or SSL to protect the connection.
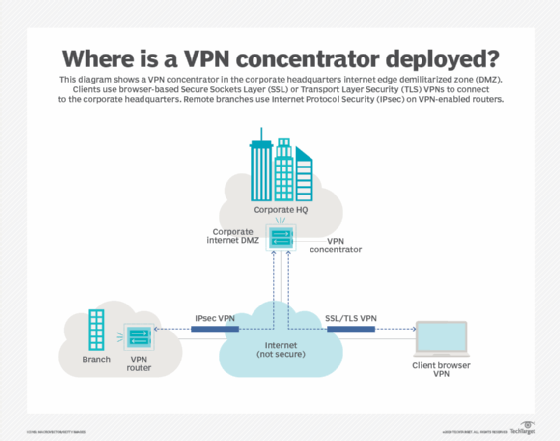
End-node gadgets in the remote location do not need VPN clients because the gateway deals with the connection. A lot of site-to-site VPNs connecting over the web usage IPsec.
What Is Vpn - Virtual Private Network Definition - Vpn Types
resource that talks about what vpns are
In a mobile VPN, the server still sits at the edge of the organization's network, making it possible for safe and secure tunneled gain access to by authenticated, licensed customers. Mobile VPN tunnels are not connected to physical IP addresses, nevertheless. Instead, each tunnel is bound to a sensible IP address. That logical IP address stays to the mobile phone.
Hardware VPNs offer a number of benefits over software-based VPNs. In addition to offering boosted security, hardware VPNs can provide load balancing for big client loads. Administration is managed through a web internet browser interface. A hardware VPN is more pricey than a software-based one. Because of the expense, hardware VPNs are more practical for bigger businesses.
Paid vendor choices tend to be suggested more frequently than totally free ones. Some VPNvendors, amongst numerous, consist of the following: contains a strong collection of security features with a big collection of servers. Nord, VPN has features such as Tor browser connections for confidential web surfing, while maintaining a strong position on customer privacy.
What Is A Vpn?
Still, it is usually considered a good VPN service. It has strong privacy and details practices focused on security and offers additional features such as split tunneling.
VPNs are legal in the United States, but users and companies ought to check if they are legal in particular nations. Many VPNs provide extremely similar innovations, so it can be hard to choose which VPN will work best. Paid VPN services tend to be more relied on and include more security features.
Around 2017, internet users in the United States found out that ISPs might gather and sell their browsing history, and net neutrality ended up being an idea people had to combat for-- and efficiently lost. An expense was passed by the U.S. House of Representatives in 2019 to restore net neutrality, however was eventually blocked by the Senate.
Wtf Is A Vpn?
With this understanding, using VPNs ended up being a more legitimate need for individuals.
Extranet-based site-to-site In the context of site-to-site configurations, the terms and are used to explain two different usage cases. An intranet site-to-site VPN explains a setup where the websites linked by the VPN come from the very same organization, whereas an extranet site-to-site VPN joins sites belonging to numerous companies. Normally, individuals connect with remote access VPNs, whereas businesses tend to utilize site-to-site connections for business-to-business, cloud computing, and branch workplace circumstances.
(MPLS) performance blurs the L2-L3 identity. Consumer (C) gadgets A gadget that is within a consumer's network and not directly linked to the service supplier's network. C devices are not mindful of the VPN.
Sometimes it is just a separation point between supplier and client duty. Other suppliers permit customers to configure it. Service provider edge gadget (PE) A gadget, or set of devices, at the edge of the provider network that links to customer networks through CE devices and provides the company's view of the customer website.
Supplier gadget (P) A device that runs inside the service provider's core network and does not straight interface to any customer endpoint. It might, for example, provide routing for many provider-operated tunnels that come from different customers' PPVPNs. While the P device is a crucial part of executing PPVPNs, it is not itself VPN-aware and does not maintain VPN state.
What Does Vpn Stand For?
1q LAN trunking to run over transportations such as Metro Ethernet. As utilized in this context, a VPLS is a Layer 2 PPVPN, emulating the full functionality of a conventional LAN. From a user viewpoint, a VPLS makes it possible to adjoin numerous LAN sections over a packet-switched, or optical, service provider core, a core transparent to the user, making the remote LAN sections act as one single LAN.
PW is comparable to VPLS, but it can supply different L2 protocols at both ends. In contrast, when aiming to offer the appearance of a LAN adjoining in between 2 or more areas, the Virtual Private LAN service or IPLS would be suitable.
This section talks about the primary architectures for PPVPNs, one where the PE disambiguates duplicate addresses in a single routing circumstances, and the other, virtual router, in which the PE consists of a virtual router circumstances per VPN. The previous approach, and its variations, have acquired the most attention. Among the difficulties of PPVPNs involves various customers utilizing the exact same address area, specifically the IPv4 private address area.
What Is A Vpn? How Does It Work And Why Do You Need ...
A restriction of conventional VPNs is that they are point-to-point connections and do not tend to support broadcast domains; therefore, interaction, software, and networking, which are based upon layer 2 and broadcast packages, such as Net, BIOS utilized in Windows networking, might not be completely supported as on a regional area network. A VPN does not make one's Internet "personal". Users can still be tracked through tracking cookies and gadget fingerprinting, even if the user's IP address is hidden. A VPN can log the user's traffic, however this depends on the VPN service provider. A VPN does not make the user immune to hackers.
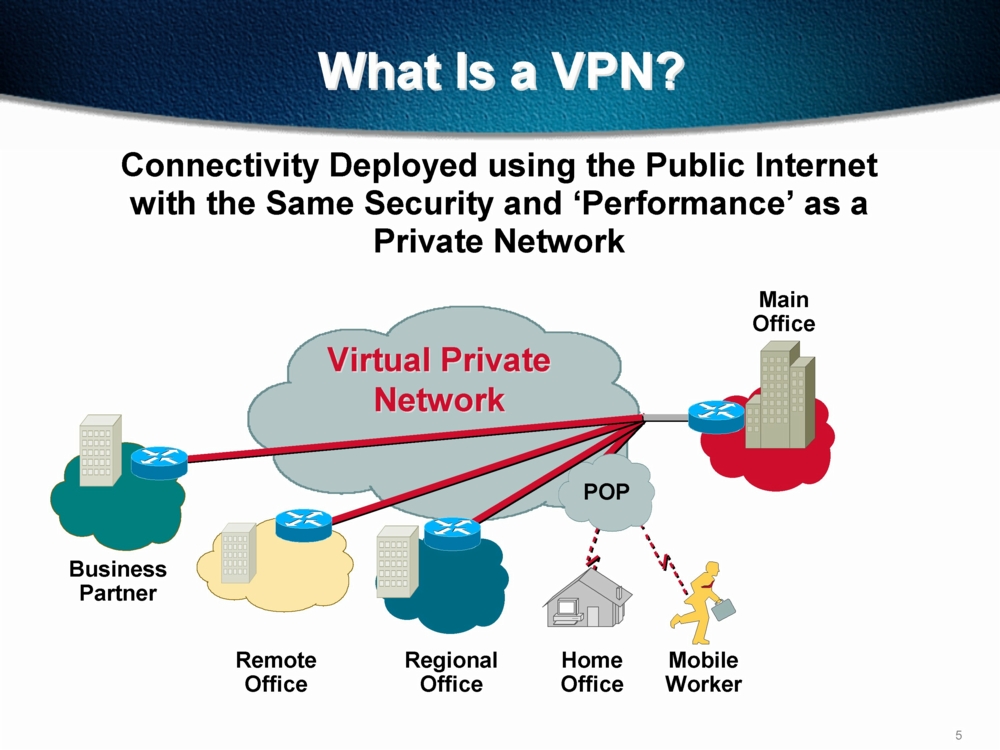
Prior to we dive directly into the inner functions of a VPN, it is a great idea to acquaint yourself with the basics of what a VPN is and what it does. The acronym VPN represents Virtual Private Network. As the name suggests, it offers users with a virtual network that is personal so that they can link to the internet in a manner that is safe and safe.
We extremely advise you read this short article for a more extensive explanation of a what a VPN is before you read this one, however here's a brief guide in any case. How precisely does a VPN do that? A VPN works by routing your gadget's internet connection through your chosen VPN's private server rather than your web service company (ISP) so that when your data is sent to the web, it comes from the VPN instead of your computer.
What Is A Vpn And Why Do You Need One?
This implies that your data is changed into an unreadable code as it takes a trip between your computer system and the server of the VPN.Your gadget is now seen as being on the same local network as your VPN. Your IP address will in fact be the IP address of one of your VPN Provider's servers.
It uses an application that develops an encrypted connection to the private network that you can then use to connect to the web at big. Some VPNs work as an internet browser add-on. There are a huge selection of add-ons you can install to internet browsers like Google Chrome or Firefox, while Opera comes with an integrated VPN.
This is perfect if you have numerous gadgets you wish to secure as it will secure every device linked to the router, saving you needing to install the VPN individually. Additionally, you'll just need to check in as soon as; your router will always be linked to your VPN.Connecting your router to a VPN isn't as difficult as you might think.
A Beginners Guide To Vpns - What Is A Vpn?
The most convenient type of router to get is one that is designed to support VPNs right now, without you having to do anything more technical that entering your VPN information. These routers can be a little more pricey than routine routers, but the convenience deserves it. Organizations frequently use a remote-access VPN for employees who work remotely.
This is a custom-created solution that needs personalized advancement and heavy IT resources. So we've discussed how a VPN works and some various ways to implement a VPN, but why precisely should you utilize a VPN? The majority of people will probably agree that the standard tenets of a VPN are an advantage.
That said, many individuals delay getting a VPN, considering it inessential or, worse, unneeded. A good way of illustrating the necessity of a VPN is to show simply how exposed you are when your internet connection is not encrypted.
Virtual Private Network
By not utilizing a VPN, you're not quite shouting your most delicate information from the roofs, but it is a little like leaving your front door open with your individual information conveniently set out on a table right inside the door. Perhaps you have good, sincere neighbors that won't come in and take what is important.
Table of Contents
- – What Is A Vpn?how Does It Work?
- – What Is A Vpn And How Does It Work?
- – How Does A Vpn Work?
- – What Is Vpn - Virtual Private Network Definit...
- – What Is A Vpn?
- – Wtf Is A Vpn?
- – What Does Vpn Stand For?
- – What Is A Vpn? How Does It Work And Why Do Y...
- – What Is A Vpn And Why Do You Need One?
- – A Beginners Guide To Vpns - What Is A Vpn?
- – Virtual Private Network
Latest Posts
Best Vpns For Freelancers And Remote Workers: Protect ...
18 Best Vpn Services To Protect Your Online Privacy + ...
16 Best Vpn For Android & Ios In 2022 [Free & Paid]
More
Latest Posts
Best Vpns For Freelancers And Remote Workers: Protect ...
18 Best Vpn Services To Protect Your Online Privacy + ...
16 Best Vpn For Android & Ios In 2022 [Free & Paid]